The potential emergence of quantum computers and their effect on the Bitcoin network is a very old and tedious debate, rife with FUD, drama and scammers always ready to sell their snake oil. While I don't have anything interesting to say about quantum mechanics or whether these computers are vaporware or just around the corner I am of the opinion that nodes can mitigate very efficiently the problems caused by technology that is capable of breaking the ECDSA algorithm, and even that these computers (if they ever materialize) will also benefit Bitcoin in several ways. This is what I want to explore today in this article.
For the sake of argument we'll assume that we're in the most "pessimistic" scenario imaginable: that Cryptographically Relevant Quantum Computers (CRQC) are only 5-10 years down the line, that they'll be able to derive ECDSA and Schnorr private keys from public keys in a few seconds, and that the energetic cost to do this computation once these computers are operational will be negligible. We'll further assume that a suitable quantum-resistant signature scheme for Bitcoin won't be devised nor soft-forked into the protocol until years after CRQCs are operational.
I have no opinion on how likely or unlikely this scenario is, but if a proposal can keep the Bitcoin network from breaking completely in this scenario it should also be effective in any other (milder) scenarios.
So why are quantum computers dangerous again?
A sufficiently advanced QRQC is able to recover the private key from any ECDSA or Schorr public key, an operation that is currently impossible because classical computers would take an inordinate amount of time to do this.
There are two types of Bitcoin addresses that expose their public key bare when an UTXO is created: P2PK and P2TR key-path spends. P2PK was the first address type and only a handful of people used it in the early days of Bitcoin, most notably Satoshi's mining rewards. P2TR key-path on the other hand is the most common address type in the UTXO set nowadays.
All other address types lock sats to the hash of a public key, not the public key itself. In this case the recipient reveals the public key (along with a valid ECDSA signature) when he creates a transaction that spends that UTXO. Quantum computers cannot reverse hashes because hashing data is a destructive operation, there's simply no way to go backwards.
The BIP-360 proposal differentiates between "short exposure" and "long exposure" quantum attacks, and it's important to understand this distinction.
Long exposure attacks are attacks on public addresses that are permanently exposed on the blockchain. This includes all P2PK, P2TR key-path and all other address types that have been spent at least once. A CRQC has as much time as it needs to crack these public keys.
A short exposure attack is an attack on a public key that has just been revealed by the original owner of the private key, and is sitting in the mempool pending confirmation. These attacks have a very short window of opportunity (normally minutes to an hour, depending on how fast blocks are found and the transaction fee). We assumed that our CRQCs can crack public keys instantly, so these are feasible in our scenario. A CRQC operator can crack public keys from the mempool, then efficiently replace the legit transactions with their own RBF transcation (Replace By Fee) that spend the same UTXOs but pays a bit more fees.
In general, a bitcoiner who doesn't use Taproot singlesig addresses and doesn't reuse his addresses is not vulnerable to long exposure attacks. However he is still vulnerable to short exposure attacks, as CRQCs operators can RBF his outgoing transactions and steal the sats before their legit transactions are confirmed at least once.
Won't somebody please think of the children?
I hold the radical idea that bitcoiners don't need to worry about long exposure attacks at all.
The main reason for that is that we rightfully never considered to make any protocol changes for the sake of the people who trusted third party custodians that rugged them, or who got their keys stolen in a computer hack or entered their 12 words to a phishing site. Similarly, to wantonly leave exposed for a long period of time your unspent bitcoin public keys should be treated no different than sharing your seed with an online scammer.
What about Satoshi's coins (they're in P2PK outputs), dead people or those funds whose keys were simply lost? I think of these coins as seabed treasure. Their original owners are no longer with us or they lost control on these coins irrevocably, so they're free game to anyone who can recover those keys (assuming the public key of the address is exposed).
Again, to protect themselves from long exposure attacks bitcoiners only need to avoid reusing addresses, a well known good practice that is even mentioned in the whitepaper. Those who fail to do so can be taught to stop doing it by CRQCs. Therefore the scope of an emergency quantum protection proposal for Bitcoin is only to thwart short exposure attacks.
Without further ado:
BIP-369: Turn off Replace By Fee for transactions spending from quantum-vulnerable address types
Recall that a bit earlier I said that the last step of a short exposure quantum attack is RBFing your legit transactions in the mempool, a familiar operation to most seasoned bitcoiners.
However, as convenient as RBF is to bump mining fees when there is congestion it did not exist from the start of Bitcoin, and the network can work without it.
The implementation of RBF removal is very simple: whenever a node receives a transaction that conflicts with another already in the mempool it discards it right away instead of considering RBF rules for replacement. Conceptually it's the same as a spam filter.
If all the honest node operators in the network disabled RBF a quantum attacker would not be able to propagate his replacement transactions, and miners would not pick them for inclusion in their block templates. His only recourse would be to mine the replacement transactions himself with his own hashrate, but even at very high hashpower 99% of the time the legit transactions in the mempool will confirm before the attacker can find any block, such is the nature of mining.
Another avenue of attack that a quantum computer could try would be running a normal Bitcoin node and try to compute the private keys of new transactions as soon as it sees them and hope to broadcast the replacements faster than the originals. But inherently the original transactions will have a head start and reach most mempools first.
While it is not a perfect solution it is very low effort for defenders, and the friction introduced should be enough to incentivize CRQC operators to focus their efforts on long exposure attacks.
The loss of RBF doesn't need to be permanent. Once a quantum safe address type is discovered and introduced into the protocol that is not vulnerable to long nor short exposure attacks, Bitcoin nodes could safely reintroduce RBF rules for transactions spending exclusively from these new address types.
Common Objections
Disabling RBF is not incentive compatible
A simplistic analysis can reach the conclusion that disabling RBF is not possible in practice because miners will always prefer to confirm transactions paying more fees than those that pay less fees. In fact mining nodes already relaxed their spam filters a decade ago to allow RBF organically!
However this happened because RBF was perceived to be all upside and no downside. On a CRQC world, permitting RBF is as bad as mining poison transactions today. And fees earned on a broken network that becomes unusable to everybody are not worth anything anyway.
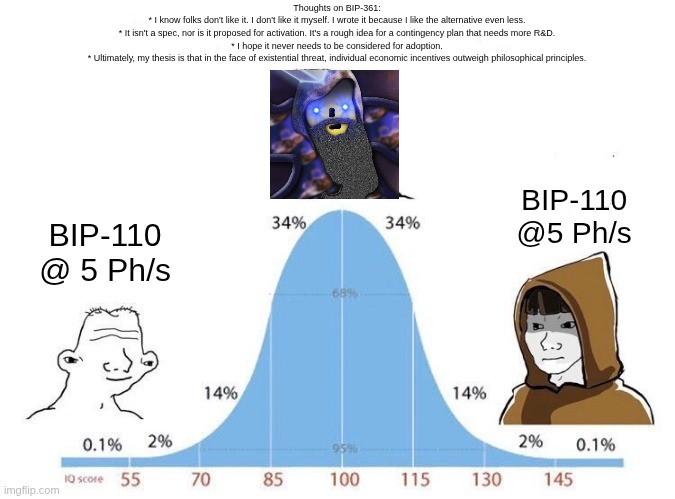
A single large pool keeping RBF would make this moot
Currently 5 mining nodes run by 5 large mining pools find 90% of the blocks. If one or several of these big stakeholders was skeptic about CRQCs and didn't want to relinquish RBF income this approach would not work in practice.
Most people don't know this at the time of writing, but the mining node count of the Bitcoin network is starting to decentralize and hashrate markets are starting to develop and mature. In the next 5-10 years mining decentralization will have improved a lot and I don't expect we'll have such large points of failure in the mining landscape. It will be "part of the culture" of Bitcoin to control 0.5 to 10 Ph/s of hashrate with your own node as the ultimate act of sovereignty that a Bitcoin user can achieve.
If you don't believe me or don't get it, my good friend Pablo found time to explain this in his personal blog. I highly recommend node runners to read My First Petahash, and to consider looking into the new field of industrial-scale home mining.
Quantum attackers can still mine
Yes, and they will have enough coins from successful long exposure attacks to rent significant quantities of hashrate. But as already explained it's just simpler and easier to do long exposure attacks. Even once long exposure coins run out and they might want to focus on short exposure theft, finding blocks is much harder than confirming transactions.
Some L2 protocols depend on RBF
Tough luck, the L1 is more important. Offchain protocols should adapt and use alternative techniques such as CPFP, or be quick to adopt quantum-safe address types once they become available.
Broadcasting very valuable transactions is still risky
Admittedly, even without widespread RBF it will still be somewhat risky to broadcast very valuable transactions spending thousands of coins.
For this reason I predict some miners will specialize in mining transactions privately at a premium. Another option will be for interested users to rent the hashrate and mine these transactions privately by themselves.
It's still possible to send sats to spent addresses
Disabled RBF protects yourself from quantum attackers replacing your own outgoing transactions. However nothing stops someone from sending sats to an already spent address, and then quantum attackers could spend this UTXO with a CPFP transaction.
Bitcoin wallets would need to adapt to this reality by pushing back (or outright refusing) to broadcast transactions that send coins to already spent addresses.
Similarly if a user has several UTXO to the same address (like e.g. OCEAN mining rewards), wallets should also refuse to spend these UTXO unless they're spent all at once in the same transaction.
But this will still crash the price of bitcoin
Yes, a lot of people will panic at the first signs of long exposure attacks and get rid of large quantities of bitcoin. However, they will be too panicked to notice that short exposure attacks will still be very rare in practice.
And like most bitcoiners, I too like generationally cheap censorship resistant orange coins.
Benefits of quantum computers to the Bitcoin network
When we talk about quantum computers in the context of Bitcoin people always focus on the doom and gloom, but there are also benefits. I already mentioned that I consider temporary low fiat price a good thing that I'll be fully taking advantage of (if or when the time comes).
There's also the implicit enforcement of not reusing spent addresses, by threat of theft.
Another aspect that most people miss is that the UTXO set is not in great shape:
Tbh I'd be fine with a quantum computer attacking quantum-vulnerable Bitcoin addresses.
— Extractive Ghost of Unhosted Marcellus 👻 (@oomahq) March 31, 2026
If I had such a computer I'd consolidate all the Taproot UTXOs holding less than 2100 sats and keep the corn as payment for the service of cleaning up the UTXO set.
At the time of writing about 50% of the UTXOs in the UTXO set are Taproot leftover dust from the ongoing spam attacks of the last 3 years. A CRQC operator would be able to reclaim all these UTXOs if their owners don't clean them up by themselves.
The oldest spamming technique is to send coins to fake bare public keys. These UTXOs are also a burden to the UTXO set and again, a CRQC can turn fake public keys into real public keys by finding their private keys that nobody had ever known.
Cleaning up the currently bloated UTXO set would be a boon for node runners, as a smaller UTXO set makes a node lighter on computing resources.
In conclusion
Quantum computers will be a very useful technology to humanity (if they're realistic) and Bitcoin will survive the disruption they'll cause once they're among us.
If you're a Bitcoin noderunner concerned about quantum computing don't reuse your own addresses, and when the time comes where there are signs of their existence just disable RBF from your node. In the meantime let the mathematicians work on devising quantum-safe signature schemes for as much time as they need.
Also, realize why the usual suspects want us to lose our minds with the same trite quantum FUD of yesteryear at precisely this point in time:
Until next time!
Unhosted Marcellus
Bitcoin node runner and home miner



Related Posts
Mapping Stats on Bitcoin Professional Frontier
Jan 27, 2026
New Year's greeting 2026: 12k-Basti and the last Fiat illusion
Jan 02, 2026
The plebs who make Bitcoin shine
Dec 28, 2025